CSRF Error on custom action
Question
When I try to use my custom action I get an error and seems the action is not available, what can I do? The error is
[CsrfGuard] - potential cross-site request forgery (CSRF) attack thwarted ....
Answer
Checking CSRF token
Actions are protected against CSRF attacks and must contain a valid CSRF token to be executed. All URLs ending with .do are checked.
When calling an action from a jahia page, the token should be automatically added and you should not worry about it. However, if it's not the case, you can verify why it's not passed.
First, check that the CsrfServlet is correctly called in your page by checking the HTML source :
<script type="text/javascript" src="/modules/CsrfServlet"></script>
This javascript detects forms and links and will add the token. It's added by a filter and should be in all pages served by Jahia.
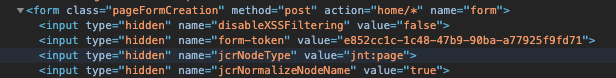
- In forms, a hidden field is added :
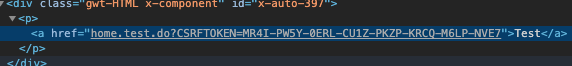
- In tags containing src or href attribute, the token is added in the URL :
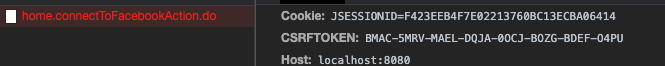
- For XHR calls, the token is transparently added into an HTTP header when the call is executed :
Finally, check in your browser, that when calling the action, the token is properly added. If it not the case, your action is maybe called with a different method. You can debug the javascript in /modules/CsrfServlet to see what is happening.
Disabling CSRF-guard for this action
As a last resort, you can add your action to the CSRF guard allow list. This may be needed if the action is called by a command-line client or another server. In that case, additional security like IP filtering can be added to ensure the action is not called by a malicious third-party.
The non-permanent way
You can configure it for your actions using a configuration file. One way to do it is from the Jahia tools --> OSGI console, there you have the possibility to change the config (under OSGI - Configuration):
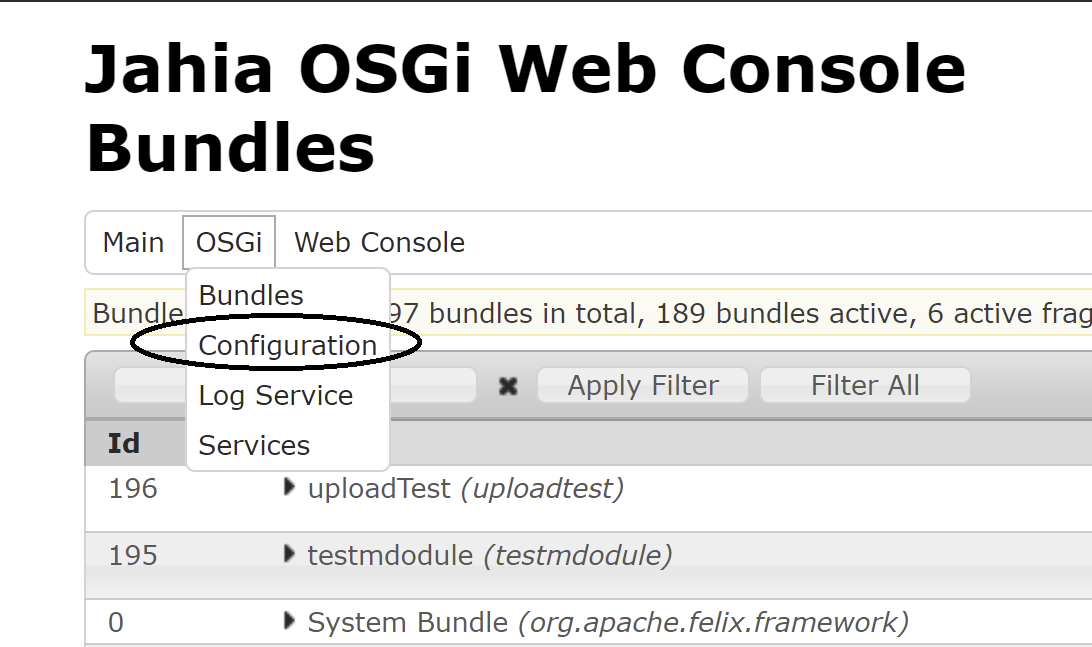
There you have to search for the org.jahia.modules.jahiacsrfguard-default.cfg, when you click on it the configuration pops up:
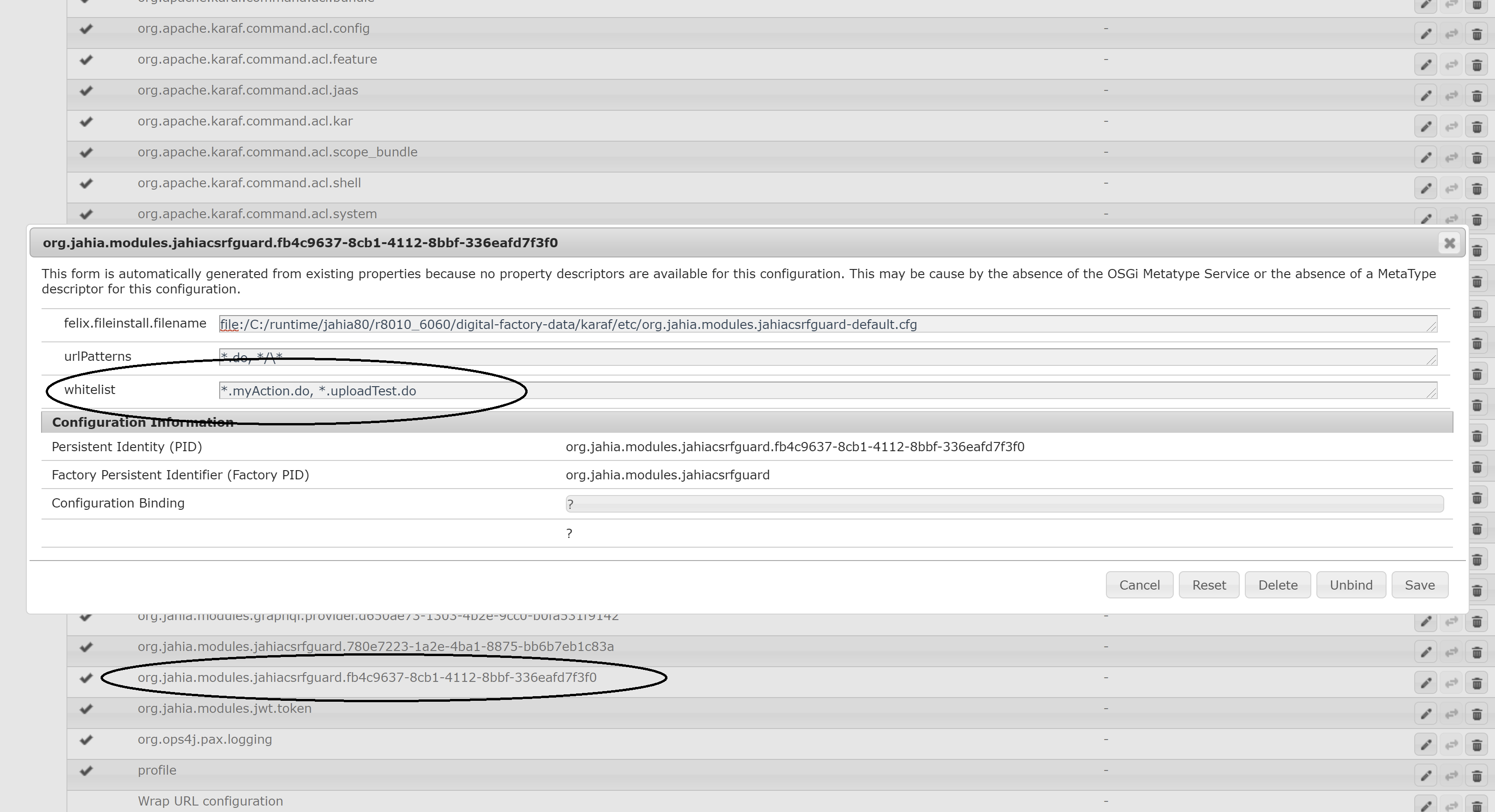
There you should see a whitelist. By default, *.myAction.do will be there, and you can comma-separated add other actions to this whitelist, for instance in my example I added *.uploadTest.do
After saving this config, it should be deployed and the action should work as expected.
The permanent way
A configuration file can be packaged directly in your module. This is the best way to allow CsrfGuard executing your actions as these settings will be used on module deployment. Here is a quick way to do it:
- First create a new configuration folder
src/main/resources/META-INF/configurations - Create a new file
org.jahia.modules.jahiacsrfguard-yourModule.cfgin this folder. Note this filename needs to be unique as it will be deployed in yourdigital-factory-data/karaf/etc. So we suggest replacing yourModule with the name of your module. So for instance if your module name is test-module then you should create such a filesrc/main/resources/META-INF/configurations/org.jahia.modules.jahiacsrfguard-test-module.cfg - Edit this new configuration file, and whitelist all your action URLs with such a line:
whitelist = *.action1.do,*.action2.do
Allow GET method
By default, all the actions are restricted to POST. You can explicitly declare that GET is allowed in your spring file with requiredMethods="GET,POST"
Override CSRF Guard configuration
Since versions 1.5.0 and 2.4.0 of the jahia-csrf-guard module, you can override the csrfguard properties in /karaf/etc/org.owasp.csrfguard.cfg (Note that the configuration should be taken on the fly without restart, but it can take up to 60 seconds until they are picked up, they should be automatically propagated and effective around the cluster, also on restarts).
For instance with
org.owasp.csrfguard.Enabled = true
you can (temporarily) disable the CSRF filter without having to stop the jahia-csrf-guard module.